Setting up the OpenTelemetry Collector in the Azure Kubernetes Service (AKS) is really easy, but there are pretty significant nuances that make it feel like it can't work out of the box. That said, they're pretty easy to get around without you having to create your own Helm charts.
Deploying a Secure OpenTelemetry Collector Azure Container Apps with Pulumi
In my last post, I described how you can build OpenTelemetry Collector container images that are secure by default. In this post, we'll take it a step further by building and pushing that image to Azure Container Registry and hosting it in Azure Container Apps. There is a Github repository if you just want to... Continue Reading →
Building a secure OpenTelemetry Collector
The builder itself is solid, and I use it all the time to build custom images, however, I've been striving for a way to build this easier in pipelines and make it more accessible to people.
Creating an AKS cluster with WebApplication Routing using Pulumi
In this post, I'll go through how to get a basic AKS Cluster up and also how to add WebApplication Routing so that you can get an automatic single ingress which is routed using domains and paths set as annotations.
I finally found a use for Logging in .NET!
Log are finally useful… for debugging tracing errors By now, you’re probably aware of my feelings towards logs, or more specifically logs created by your application. That said, I’ve finally found a use for them! Why do I hate logs? The short answer is I don’t. The longer version is that I don’t see any... Continue Reading →
Trace Propagation and Public API Endpoints in .NET – Part 1 (Disable All)
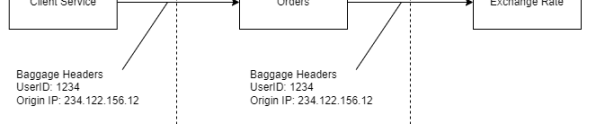
Trace Propagation is the true super power of Production debugging of distributed systems, as the movies say, with "With great power, comes great responsibility".
Creating an AKS cluster with an Application Gateway and Pulumi
I'm a huge fan of Pulumi and I've had the need to create an AKS cluster recently so thought I'd give it a go with Pulumi. It turns out that adding an Application Gateway isn't the easiest thing to do. What is Application Gateway? Azure Application Gateway is the Layer 7 (HTTP level essentially) load... Continue Reading →
Does OpenTelemetry in .NET Cause Performance Degradation?
Contrary to Betteridge’s Law of Tabloid Headlines, the answer is “yes,” but context is important. I get this question so often that I thought it was time to get some stats on it.
12 Factor Apps and Modern Observability
These are great goals, and the intent is still valid. However, this factor does go into implementation details of using stdout to push logs, and this is where I think we've evolved as an industry.
Parsing Azure Resource Id’s with the ResourceIdentifier class
I've been working with Azure Diagnositc logs recently, and part of the data that comes out of them is something azure calls a "ResourceId". This is used to uniquely identify the resource in Azure. It's a slash separated value that includes a hierarchal list of values.